Hello Reader,
I was reading the libbde specification again and noticed I was missing something in the screenshots I posted yesterday. Yesterday I stated the hostname of the computer that encrypted the drive was present as well as the date it was encrypted. What is being stored between those two values though is the name of the volume being encrypted.
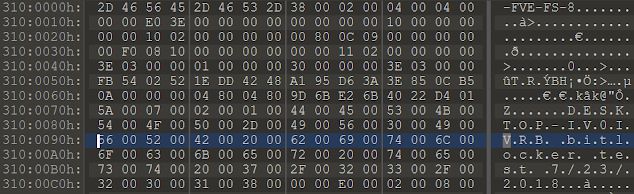
So in the first example:
I was reading the libbde specification again and noticed I was missing something in the screenshots I posted yesterday. Yesterday I stated the hostname of the computer that encrypted the drive was present as well as the date it was encrypted. What is being stored between those two values though is the name of the volume being encrypted.
So in the first example:
After the Desktop hostname you can see the Unicode string bitlocker test. This was the name of the vhd I created and formatted NTFS for this test.
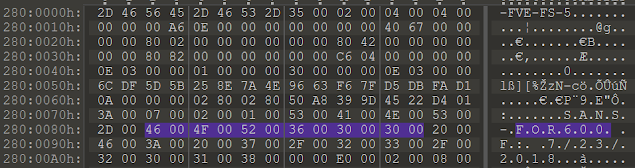
In the case that there is no volume label present, as was the example with my Bitlocker ToGo example, the drive letter it was assigned at the time of encryption will be stored as seen below:
In the above screenshot after the SANS-FOR600 string and before the 7/23/2018 string you can see F:. F: was the drive letter assigned to this volume prior to its encryption with bitlocker and the volume had no name given at the time of format.
So in total from an encrypted bitlocker disk so far we can determine:
1. The Hostname that encrypted it
2. The volume label or drive letter assigned ( if there is no volume label present) when it was encrypted
3. The date if was encrypted
4. In prior research we found we find the key identifiers of the recovery keys
Why is this useful? We can match this up in the case of external drives not only with the systems that encrypted them but also to the artifacts that show what was being accessed from these drives. In addition if you needed to look up a recovery key you could so with the hostname even if the identifier doesn't help you. Lastly you can determine when something was encrypted as it might correspond to a time when your suspect became aware of an investigation.
This is a 5-part series and make sure to check all the parts:







Post a Comment