Another week of competition is concluded and a victor has a emerged. This week we continued the video conferencing artifacts and Oleg Skulkin with his sheer persistence every week has pulled out the win!
The Question:
When looking at Zoom from a DFIR perspective:
1. Where are the artifacts?
2. What format are they in?
3. Can you recover chat history?
4. Can you recover call history?
5. Anything else you can determine?
The Winning Answer:
Oleg Skulkin (@oskulkin)
https://cyberforensicator.com/
Let’s start from
artifacts locations. This time I used two devices for testing: a Windows laptop
and a macOS laptop.
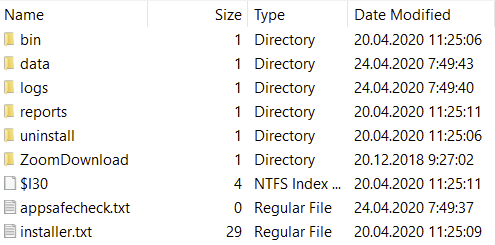
So, on Windows the
artifacts are stored under:
C:\Users\%USERNAME%\AppData\Roaming\Zoom
You can find the
following files and folders inside:
The most interesting
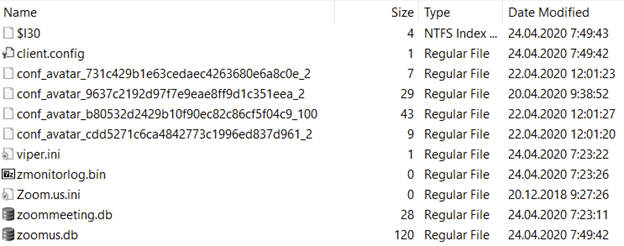
folder here is data. Here are its
contents:
At first glance we can
see two DB files, which are SQLite databases, but unfortunately both databases
don’t contain much useful information.
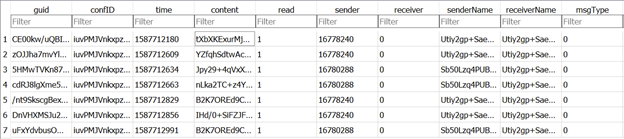
The first, zoommeeting.db, contains some info
about meetings, including the timestamps in Unix Epoch:
The next database, zoomus.db, should contain lots of juicy
artifacts as, according to Procmon, zoom.exe interacted with it very often, but
in fact – it’s almost empty. You can collect some general configuration
information from zoom_kv table. Another
table, zoom_conf_avatar_image_cache,
contains paths for conference avatar images located in the same folder. One
more table, zoom_actions_logs,
contains info about conference actions, for example, screen sharing, audio
muting, etc. Other tables in my testing were empty. I tried recover data using
multiple forensic tools as well as using hex viewer, but had no luck. It seems
Zoom doesn’t want to store anything due to recently uncovered security flaws.
As for macOS,
artifacts are located under:
/Users/%USERNAME%/Library/Application
Support/zoom.us
There are two folders
inside: data and Plugins.
The data folder
contains the same databases as Windows version – zoommeeting.db and zoomus.db,
also almost empty.
So? I couldn’t recover
neither call, no chat history. Probably, it needs much more testing.







I am finding something very similar in terms of very few artefacts. I wonder if this has been an improvement on their end in terms of security-by-design.
ReplyDelete