Update 12/6/18: It turns out that my test system had a system volume smaller than 128gb in size meaning the last access dates were enabled (setting 2). According to @errno_faiil (Maxim Suhanov) if my system driver was larger than 128gb then the last access dates would be disabled (setting 3).
Want to know more? Watch this video: https://www.youtube.com/watch?v=yHG6MEH99Z0
Hello Reader,
It looks like as of at least Windows 10 1803 a new change has come to an old registry key. The NtfsDisableLastAccessUpdate key found in 'SYSTEM\CurrentControlSet\Control\FileSystem' no longer is just a true/false 1/0 value. It now has four possible values stating how the access dates in NTFS were enabled or disabled.
Looking at my laptop's registry I can see the following value is currently set:
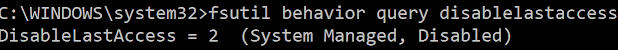
which leads to the question of... what does 80000002 mean? Luckily fsutil will translate the current value for us:
So the 8 appears to be some kind of upper bit masking while the 2 is the value set letting us know that NTFS Access updates are currently disabled by system policy.
Checking the set behavior command in fsutil shows us all the possible documented options:
As you can see we've moved from two possible states (on/off, true/false, 0/1) to four. The system is now tracking if the user or the system has enabled or disable last access dates in NTFS.
Why? I have no idea currently but it certainly does add more context to the decision. So all of you who have tools that interpret this value will need to update your tools!
Also Read: Daily Blog #556
Want to know more? Watch this video: https://www.youtube.com/watch?v=yHG6MEH99Z0
Hello Reader,
It looks like as of at least Windows 10 1803 a new change has come to an old registry key. The NtfsDisableLastAccessUpdate key found in 'SYSTEM\CurrentControlSet\Control\FileSystem' no longer is just a true/false 1/0 value. It now has four possible values stating how the access dates in NTFS were enabled or disabled.
Looking at my laptop's registry I can see the following value is currently set:
which leads to the question of... what does 80000002 mean? Luckily fsutil will translate the current value for us:
So the 8 appears to be some kind of upper bit masking while the 2 is the value set letting us know that NTFS Access updates are currently disabled by system policy.
Checking the set behavior command in fsutil shows us all the possible documented options:
As you can see we've moved from two possible states (on/off, true/false, 0/1) to four. The system is now tracking if the user or the system has enabled or disable last access dates in NTFS.
Why? I have no idea currently but it certainly does add more context to the decision. So all of you who have tools that interpret this value will need to update your tools!
Also Read: Daily Blog #556









Good catch and thanks for the post.
ReplyDeleteThanks for reading!
DeleteAs to the why? I think for anti forensics this is a good detection to see if CAW (create access write) was tampered
ReplyDeleteI don't disagree that its a detection, just seems like a strange decision to turn it on with a gigabyte limit constraint.
Delete