Hello Reader,
This week a new champion emerges and enters the winners circle. Congratulations to Oleg Skulkin who grabbed a win this week with his testing! Make sure to come back tomorrow to see next weeks' challenge for your chance at $100!
This week a new champion emerges and enters the winners circle. Congratulations to Oleg Skulkin who grabbed a win this week with his testing! Make sure to come back tomorrow to see next weeks' challenge for your chance at $100!
The Challenge:
We've tested what happens for copies to NTFS drives. Now let's change it up. What changes occur to files when you copy and paste as well as cut and paste to a FAT32 drive
The Winning Answer:
Olegl Skulkin
I created 6 files, 1 DOCX, 1 TXT, 1 JPG on an NTFS volume for copying, and 1 DOCX, 1 TXT, 1 JPG for cutting and pasting. I used Windows 10 both for copying and cutting, and a freshly formatted FAT32 flash drive.
I created two folders on the flash drive – “copy - paste” and “cut - paste”. I copied and pasted first three files to “copy - paste”, and next three files to “cut - paste”. Then I imaged the flash drive with FTK Imager (4.1.1.1) and used Autopsy (4.9.0) to examine the image.
Here are the results:
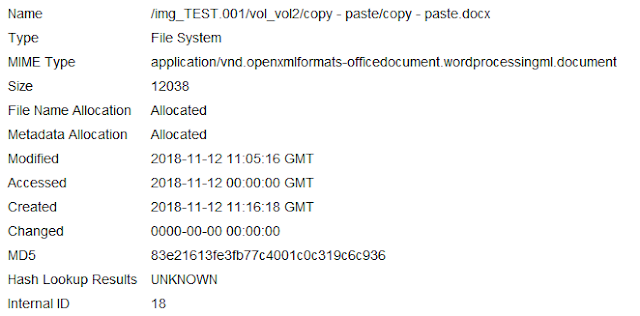
The DOCX file saved its Modified timestamp, lost time for Accessed, and its Created timestamp changed. Despite the fact I used UTC as the timezone in Autopsy, the timestamps were shown in UTC +3.
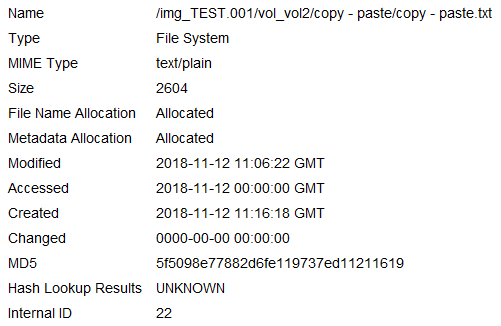
The same results were observed for the TXT file:
And for the JPG file:
As for cutting and pasting, the DOCX file saved its Modified and Created timestamps, but lost time for Accessed timestamp (again, timestamps are in UTC +3):
The same happened with the TXT file:
And with the JPG file:
Results
Copy – paste:
Modified
|
Accessed
|
Created
|
Unchanged
|
Changed
|
Changed
|
Cut – paste
Modified
|
Accessed
|
Created
|
Unchanged
|
Changed
|
Unchanged
|


.png)
.png)
.png)
.png)





Post a Comment