Hello Reader,
Well this weeks challenge had a lot of submissions! It was very tough picking a winner but as the rules state the most complete answer wins. When it comes to complete answers this week Kevin Pagano did the most testing of extended mapi attributes in his testing with screenshots and a follow up email to fill in even more.
What I liked about Kevin's answer that put him over the top is that he not only submitted PR_CLIENT_SUBMIT_TIME as most people did. He also went in and found other Extended MAPI entries that could be related even testing a deferred delivery mechanism I haven't even thought to test yet!
So well done Kevin Pagano you are this weeks winner.
Here was this weeks challenge:
The Challenge:
Extended MAPI records metadata around what actions occur against an email message inside of Exchange and Outlook. What within an email message sent from Outlook and connected to an Exchange server would allow an examiner to determine when an email was sent from the system they are examining presuming they found the message in the sent folder within the mailbox.
Here is Kevin Pagano's winning submission.
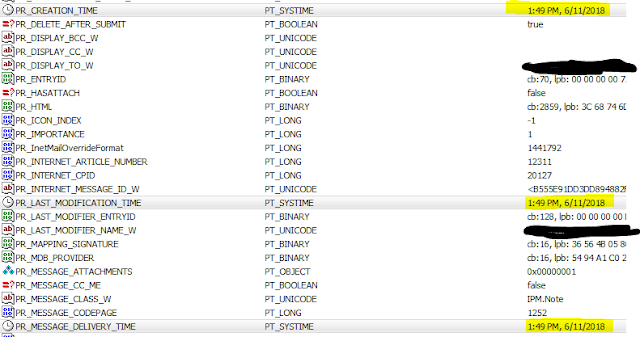
In a test by sending an email to myself, the PR_LAST_MODIFICATION_TIME matched that of the PR_CREATION_TIME field. Since sending an email creates a brand new email entry in your mailbox, thus syncing the creation time of the email with when it was last modified before it being sent out. All of these times are in UTC.
In another test marking a Sent email to unread this did update the PR_LAST_MODIFICATION_TIME field to reflect when it was set to unread.
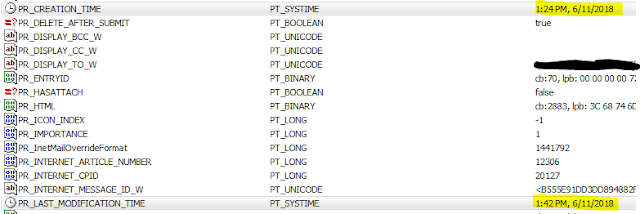
A third test for curiosity sake was done. While selecting to do a delay delivery of an email, we see that the PR_MESSAGE_DELIVERY_TIME is set to when the user hit send on the email, while the PR_CREATION_TIME is set to when the email was created in the Sent Folder (2 minutes later). You can also see the PR_DEFERRED_DELIVERY_TIME as well when the user set it to be sent.
This would seem to indicate that the PR_MESSAGE_DELIVER_TIME is when the user hit send in Outlook while the PR_CREATION_TIME would be your closest match to when the email was officially sent through Exchange creating the Sent email in the Inbox.
In doing more research, the PR_CLIENT_SUBMIT_TIME field seems to be a better indicator when the user submits an email to be sent. While the PR_MESSAGE_DELIVERY_TIME matched times when the emails were sent this could be different in other instances where the network connection is slower and has more hops to jump between Exchange servers.
Also Read: Daily Blog #394








Post a Comment