Hello Reader,
I'm intending for this to be the last blog in the series, at least for now. Today let's look at recovering past interaction with files accessed from MTP devices. You may ask yourself why what we've seen so far isn't enough to determine past interaction, well there are several reasons:
1. Windows 7 (haven't tested other versions at this point) will delete the contents of the WPDNSE directory on reboot.
I'm intending for this to be the last blog in the series, at least for now. Today let's look at recovering past interaction with files accessed from MTP devices. You may ask yourself why what we've seen so far isn't enough to determine past interaction, well there are several reasons:
1. Windows 7 (haven't tested other versions at this point) will delete the contents of the WPDNSE directory on reboot.
2. The MFT will only contain those WPDNSE deleted content FILE records until they are overwritten or Defrag runs, which is once a week on Windows 7.
3. Most applications will not make LNK files for the accesses.
4. Most applications will not make jumplists for the accesses.
5. The Shellbags will reveal directories on the MTP devices that were accessed but not the files themselves.
So we are left with two possible source for historical viewing after a weeks worth of time.
1. MRU keys
No record of any of these files having a MRU entry. This isn't terribly surprising as we didn't find a LNK file or a Jumplist entry for them.
2. USN Journal
The USN Journal is a great source of information here. Since the issues of GUIDs an the like are not an issue you just need to find the MFT entry numbers for the WPDNSE directory, which in my testing was 57374 and then search for all USN entries with a 57374 as the parent entry number.( If this was a real case I would also match the sequence number. ) The following is what comes back:
So now we can see that the Folder GUID '{00000025-0001-0001-0000-000000000000}' was the only directory created within our USN Journal within the WPDNSE directory. We don't have the translation to directory name here, but as we saw in the prior post we can look that up from the shellbags.
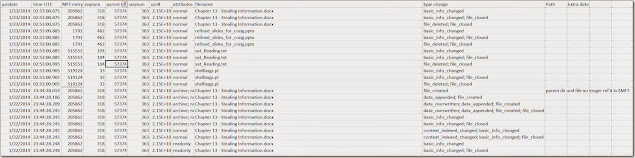
Looking deeper and now looking for all files with a parent MFT entry of 57374 which we got from the above screenshot we can see the following files were accessed from the MTP device:
So we are left with two possible source for historical viewing after a weeks worth of time.
1. MRU keys
No record of any of these files having a MRU entry. This isn't terribly surprising as we didn't find a LNK file or a Jumplist entry for them.
2. USN Journal
The USN Journal is a great source of information here. Since the issues of GUIDs an the like are not an issue you just need to find the MFT entry numbers for the WPDNSE directory, which in my testing was 57374 and then search for all USN entries with a 57374 as the parent entry number.( If this was a real case I would also match the sequence number. ) The following is what comes back:
So now we can see that the Folder GUID '{00000025-0001-0001-0000-000000000000}' was the only directory created within our USN Journal within the WPDNSE directory. We don't have the translation to directory name here, but as we saw in the prior post we can look that up from the shellbags.
Looking deeper and now looking for all files with a parent MFT entry of 57374 which we got from the above screenshot we can see the following files were accessed from the MTP device:
Now if this was an XP system you would be out of luck, so let's hope any MTP analysis you need to do is on Vista/7 or 8!
Tomorrow is the forensic lunch, try to make time to watch it live and ask questions!
Don't miss out on:







Post a Comment