Hello Reader,
This weeks Sunday Funday must have hit a cord out there as I got many great submissions. Picking a winner when there are multiple great answers is hard and I had to ask for a second opinion from the lab to come to an agreement, they were that good this week.
This weeks Sunday Funday must have hit a cord out there as I got many great submissions. Picking a winner when there are multiple great answers is hard and I had to ask for a second opinion from the lab to come to an agreement, they were that good this week.
With that said, this weeks winner is an anonymous submission whose answer shows a depth of experience that I appreciated. They answered the question well and provided some great gotchas to make note of. If you are doing mobile forensics you should read this one and check out the links provided in it.
Updated with Pictures!
The Challenge:
You are faced with an Android device where full physical imaging isn't
supported by your mobile forensics software provider. What steps would
you take to accomplish the following:
1. Locate a safe rooting mechanism
2. Test the rooting mechanism
3. Image the device
4. Manually extract the sms database
5. Parse and export to xls the sms database
1. Locate a safe rooting mechanism
2. Test the rooting mechanism
3. Image the device
4. Manually extract the sms database
5. Parse and export to xls the sms database
The Winning Answer:
AnonymousRemove the SIM and SD Cards and exploit separately. The SD Card may be encrypted but in my experience very few users enable this.Place the handset into Airplane Mode and switch off WiFi and BlueTooth.Attempt to image the device using an off the shelf tool such as the Cellebrite UFED or XRY. We will usually attempt to exploit the device logically initially and then either take a physical image or a file system dump depending on what is supported and whether the device has full device encryption enabled.If the device won't image using our standard tools we will then move on to other methods. This may be JTAG if the device is supported by the RIFF box and we have permission from the customer to take the device apart or more likely will involve rooting the device.The best source of information for all things android is the XDA Developers Forums www.xda-developers.com. The forums can be searched for a specific device and then the various rooting options explored.Rather than use the rooting exploit on the handset being investigated I would first attempt to root another handset of the same model. We are lucky enough to have access to a good library of devices but if this was not the case I would attempt to purchase one, ideally of the same make, model and network as that being investigated. I would then root the purchased handset in order to make sure the process does not unduly effect the data on the device. Only once this has been proved would I use the rooting exploit on the target device.Once the device is rooted I would ensure that USB Debugging and Stay Awake options are enabled in the developers area of the settings. The developer area is not always immediately visible but can usually be made to appear by clicking around seven times on the Build Number in the About Phone section of the options.Insert a large SD card into the device boot it up and connect the handset to a machine with the android SDK installed. The Santoku VM, downloadable from santoku-linux.com is a good choice.The command adb devices will show one device connected if all is working correctly.Type adb shell in order to gain a linux shell onto the rooted device.Type the following commands in the shell:sumkdir /sdcard/forensicscp /data/data/com.android.providers.telephony/databases/mmssms.* /sdcard/forensics (this will copy the files required for the SMS investigation. Use * in order to copy the Write Ahead Log files as well as the main sqlite database).mount (this will show a list of the devices mounted on the various directories of the file system. We are usually interested in the /data directory).
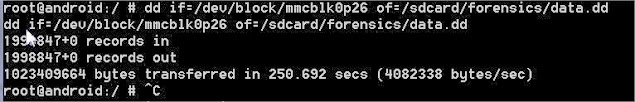
dd if={BlockDevice} of=/sdcard/foreniscs/data.dd (where {BlockDevice} = the device identified above. On my sample phone this was /dev/block/mmcblk0p26.
Ctrl-C (this will exit back to the main PC shell.)
Then use the command adb pull /sdcard/forensics . to pull the image and extracted SMS database back to the investigators machine. Or alternatively just pull the SD Card and connect it using a normal card reader to access the files.
In order to process the SMS databases I would use the epilog tool from CCL forensics as this is the only tool I know of which accurately recovers all the deleted data from SQLITE databases which use a Write Ahead Log. It comes with a number of signature files and these include those for dealing with the android SMS database. Epilog allows for exporting to Excel as well as various other formats.
Updated with Pictures!
Also Read: Daily Blog #189








Post a Comment