Hello Reader,
Another Sunday Funday behind us and a another challenger who came with a great writeup full of testing and description. This weeks winner Andy Dove is now a two time Sunday Funday winner and brought some good testing this week. I plan to spend this week delving into the host based artifacts outside of Office that Andy didn't cover.
The Challenge:
Another Sunday Funday behind us and a another challenger who came with a great writeup full of testing and description. This weeks winner Andy Dove is now a two time Sunday Funday winner and brought some good testing this week. I plan to spend this week delving into the host based artifacts outside of Office that Andy didn't cover.
The Challenge:
An employee has been terminated after a lengthy workplace investigation. After being terminated the employee has come back with a lawyer stating that a word document on their work computer will exonerate them and that they are suing for discrimination. The document appears to be a memo written by the employee's manager to the ex employee with derogatory language toward their race. The employee's manager has stated that they never wrote the document and they believe it be fraudlent.
If the employee was issued a Windows 7 system with Microsoft Word 2007 what would you do to determine:
- Which system the document with authored on
- Who was the author
- What was the last author
- If the time stamps have been altered
Two Time Winner Andy Dove!
Nice to be back to Forensics for this
week’s challenge. My first port of call
in this particular situation is to look at the Metadata embedded into each
Office File. This can be viewed quite
simply using the Windows File Properties dialog. Of particular interest in this particular
case are the internal author and timestamp fields. These internal timestamps are completely
independent of the file system values and are not affected by utilities such as
“Touch” which change MAC times. To
illustrate this I have done the following:
- Created a file in Word 2007
- Copied it onto a FAT32 formatted SD Card.
- Copied onto a different user account.
- Edited the file on the new account.
- Edited the file again and changed the Author using MS Word.
After each step I have displayed the
properties and taken screenshots.
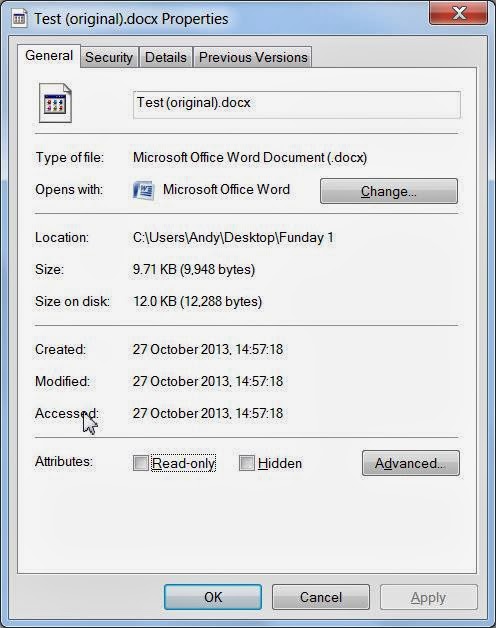
Original File
Note that in this document the internal creation time precedes the file system time. This is because the document was created within word, edited and then saved, rather than generating a new document from the Explorer right click menu.
Copied File (Unedited)
Here the file system times are again quite different to those held internally. Had this process taken place over hours or days rather than minutes this difference would highlight the document had likely been copied over onto the machine. Here the Author and Last Saved By fields also reflect the original values. Possibly of note is also that the the NTFS Modified TimeStamp value has also changed due to having been stored on a FAT32 system where the timestamp is stored with less precision.
Copied and Edited
After editing the Last Saved by field has been updated to show a new user has worked on the document.
Author Changed
Here I have edited the author field to make it look more likely that it was created by the second user.
Where was the Document Created?
In MS Office 97 a GUID based on the MAC address of the computer which created the document is embedded within the file. This is only added at creation time and is never changed on subsequent saves. I have examined all the embedded XML files in my test document and have not been able to find a similar artefact within the Word 2007 files. In this case I would revert to traditional forensic methods such as the examination of Jump Lists, Link Files, Prefetch Files and Volume Shadow Copy analysis to try and find evidence of the original file.
Interestingly the Windows file properties dialog isn’t your friend here. Although it shows an entry for computer (See below) switching to another machine and then displaying the properties will show the new computer rather than the one on which the document was created. The document shown below was created on a machine called PIGLET.
Examination on a non-Windows Machine
If examining the files on a non-windows machine it would be possible to view the embedded information by treating the file as a zip, unpacking it and opening the doc\Props\core.xml file. In the case of my original document this clearly shows the same information as shown previously:














Post a Comment