Hello Reader,
So yesterday we talked about how to recover the Facebook chats found in the Sunday Funday 10/6/13 Image, today let's move onto how to extract history from IE10. We picked IE10 for this image because Microsoft switched the history storage formats and we wanted to see how you would handle it. In IE versions prior to IE10 (IE 4-9) the user's internet history was kept in a series of index.dat files. These formats are well understood and there is a large variety of tools to parse them. However, things change and when browsers you know where in use (appshimcache, userassist, prefetch, etc..) don't have history appear in your tool of choice its time to investigate why. I've had this happen before once with chrome, click here to read how I handled it.
For IE10, and maybe IE11 I haven't tested it yet, the storage engine has switched to JetBlue extensionable storage engine 'ESE DB'. The first thing to know is that the location of the internet history has moved to
/%root%/Users/%UserName%/AppData/Local/Microsoft/Windows/Webcache
Within this directory you'll find logfiles and a file called 'WebCacheV01.dat' or V16.dat or V24.dat.
Tomorrow we'll talk about what else we can find, and then Friday we have another great Forensic Lunch!
So yesterday we talked about how to recover the Facebook chats found in the Sunday Funday 10/6/13 Image, today let's move onto how to extract history from IE10. We picked IE10 for this image because Microsoft switched the history storage formats and we wanted to see how you would handle it. In IE versions prior to IE10 (IE 4-9) the user's internet history was kept in a series of index.dat files. These formats are well understood and there is a large variety of tools to parse them. However, things change and when browsers you know where in use (appshimcache, userassist, prefetch, etc..) don't have history appear in your tool of choice its time to investigate why. I've had this happen before once with chrome, click here to read how I handled it.
For IE10, and maybe IE11 I haven't tested it yet, the storage engine has switched to JetBlue extensionable storage engine 'ESE DB'. The first thing to know is that the location of the internet history has moved to
/%root%/Users/%UserName%/AppData/Local/Microsoft/Windows/Webcache
Within this directory you'll find logfiles and a file called 'WebCacheV01.dat' or V16.dat or V24.dat.
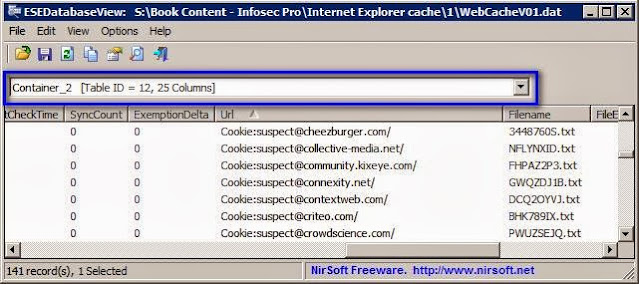
To look over this, I’ll use the Nirsoft ESEDatabaseView
application. In some cases, this
database may have to be repaired. I’ll
refer you to a TechNet website for this:
In our suspect image the file is called WebCacheV01.dat, once the WebCacheV01.dat file is loaded into ESEDatabaseView, make sure
you use the drop down box to select a table to view. Below I have “Container_2” selected, which
for me is the table for Cookies.
Tip: Make sure you select the options to format
the timestamps. Unless you’re good at
reading nanoseconds, of course.
So
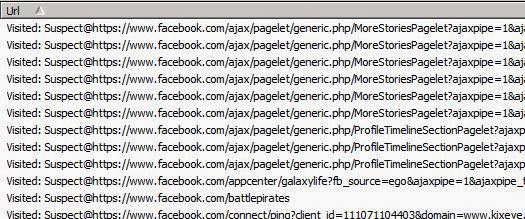
let’s take a closer look at what our suspect is browsing. Selecting the “Container_4” Table shows us
URLs that were visited. I’ll usually
start by sorting the data by the URL to target items that would otherwise be
spread out.
This will show us that our
suspect visited at least 6 pages of the icanhas.cheezburger.com website.
Continuing review of the
visited websites, we see that Facebook was accessed, too.
In
the following image, we also see access to other cheezbuger.com webpages. Sixteen more for just their “geek” pages.
One
more activity I’ll show for you is the Suspect’s access to reddit.com.
Also Read: Daily Blog #107










Post a Comment